Get Free Trial Week Developer Access, Try Before You Hire. Click Here to Claim Now
Introduction:
The information about all the objects like users, computers, and resources like files, and folders present in a company is stored in an energetic directory. The active directory is comparable to a telephone book. AD employed in arranging, providing access and supply permissions-based information. all told the network users; computers are arranged into logical hierarchical groupings levels. If you wish to authenticate or authorize the users, over a network then active directory information is employed.
What is Active Directory?
Active Directory may be a centralized database that stores the data associated with user’s passwords groups and OU's in a company. Since all the data is stored during a secure and centralized location this improves security. Microsoft has introduced the server product since it had been meant to be deployed on the server because the centralized database which will only air server hence it cannot be installed on client operating systems.
How Active Directory Works?
1. It’s a database that consists of varied Users, Groups, OUs, etc.
2. All objects are present in hierarchical order and this is often handled by LDAP (Lightweight Directory Access Protocol). That’s why AD is additionally called Directory Service.
3. Creates a site for the organization and everyone systems become a part of that individual domain.
4. Provides centralized management of all Windows systems within that domain.
5. Provides authentication and authorization service for all Users and Applications consistent with their access levels.
6. Manage the policy for each object within the enterprise (domain) using GPO (Group Policy Objects).
7. In short, Active Directory creates and manages the IT infrastructure of any organization.
Example of How AD works?
Mr. ABC joins as an HR in a company. just like the company on board him, he are given access to applications like Office 365, OrangeHRM, etc. All his details and also the applications he's given access to are recorded within the HR system. The Active Directory pulls this information from the HR system and the next time ABC wants to log in to Office 365, OrangeHRM, his access gets authenticated by the active directory. active directory acts as streamlines and provides secure authentication to applications. Active Directory Authentication using LDAP
What's LDAP (Light Weight Access Protocol)?
It is an application protocol used over an IP network to manage and access the distributed directory information service. LDAP is generally employed by applications to access a directory that contains the identity of users who can sign on. Having the applying hook up with the directory server using the user's login ID and password is usually accustomed authenticate users. It provides a customary thanks to share user information. LDAP also allows users to authenticate in external or internal systems. The LDAP protocol itself is standard and vendor neutral. However, they need implementation-specific issues, for a way the data is presented. It’s a light-weight client-server protocol for accessing directory services, specifically X.500-based directory services. This Protocol runs over TCP/IP or other connection-oriented transfer services.
It is mostly employed in Active Directory for exchange information through user queries. as an example, LDAP is employed by users to look for an object sort of a electrostatic printer. It uses the keywords to hold out an enquiry operation and identify the objects that are made possible with the assistance of its attributes.
LDAP computing follows the client/server prototype. during this scenario, the client is requesting information from the same LDAP database and also the server is, of course, the LDAP server. The server side of LDAP may be a database that has an adaptable composition. In other words, not only can LDAP store the username and password information, but it also stores the variability of attributes including address, phone number, group associations, and more. As a result, a typical LDAP use-case is to store core user recognition.
LDAP is comparable to a database but tends to contain more descriptive, attribute-based information. Data during a directory is mostly interpreted way more often than it corresponds. Directories are tuned to present quick responses to explore the behavior. it's going to have the power to copy information widely to extend availability and reliability while reducing latent period. it's many various ways to produce a directory service and different methods allow different sorts of information to be stored within the directory, various of the directory services are local, providing service to a restricted surrounding (e.g., the finger service on one machine).
Advantages of LDAP:
1. It supports multiple platforms with standard APIs for every platform.
2. The LDAP directory is distributed across multiple servers.
3. It provides easy integration with other standards like DNS.
Where can we use LDAP?
LDAP is generally used as an authorized protocol for directory services. We use LDAP to authenticate users to the online applications, NAS devices, and SAMBA file servers.
Does LDAP is secure?
To secure the services, LDAP transactions must be encrypted using an SSL/TLS connection. To set up, either use LDAPS on port 636 or StartTLS on the quality LDAP 389 port.
Below operations supported by the active directory using LDAP C#
1. Connection to Active Directory:
To connect to the AD employing a secure connection, you would like to delegate the permissions of a user account with Domain Admin permissions to the thread that's running a program.
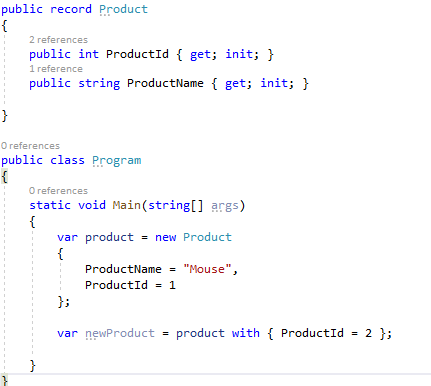
2. Check if a user exists
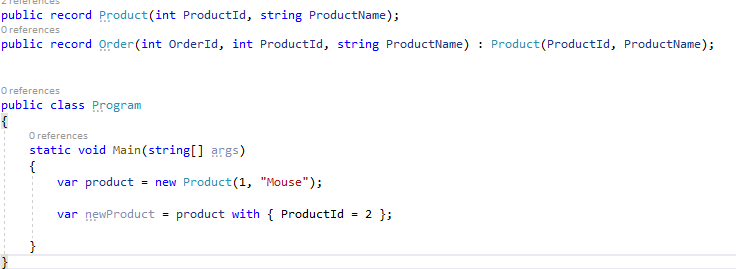
3. Set user's property
4. Set the user's country
5. Set user's password
6. Enable a user account
7. Add a user to a gaggle
8. Create the user Account
9. Update user account
10. Search users
The Directory Searcher object allows you to question the AD. the subsequent sample code inquires of AD to look all the user accounts that were modified from a given date. The results are stored during a Data Table, so you'll easily data bind them.
Conclusion
LDAP was designed as a light-weight protocol which will access directory contents. because it evolved over the years, it gained important features, like authentication and transport security. As a well-defined means to induce user information, it's found its thanks to small and large deployments.
Subscribe to Our Newsletter!
Join us to stay updated with our latest blog updates, marketing tips, service tips, trends, news and announcements!